In this post I want to go back to the basics of security design and the implementation of the security buzz words that I am quite certain that everyone has heard, such as Defense in Dept, Zero Trust, Micro Segmentation etc. With that I would like to provide an overview of a fictitious network that I have designed in VISIO to illustrate some examples of basic security boundary’s that every organization should have in place to protect their critical assets.
The Below diagram is not meant to serve as a holistic security design but rather a visual representation of what security controls could be in place. This will provide you with a security thought exercise, to get you thinking about what you can implement to gain traction in your Defense in Dept, Zero Trust and Micro Segmentation journeys. I hope that many of you are already nearing the appropriate maturity levels for your organizations.
Sample Network Security Design:
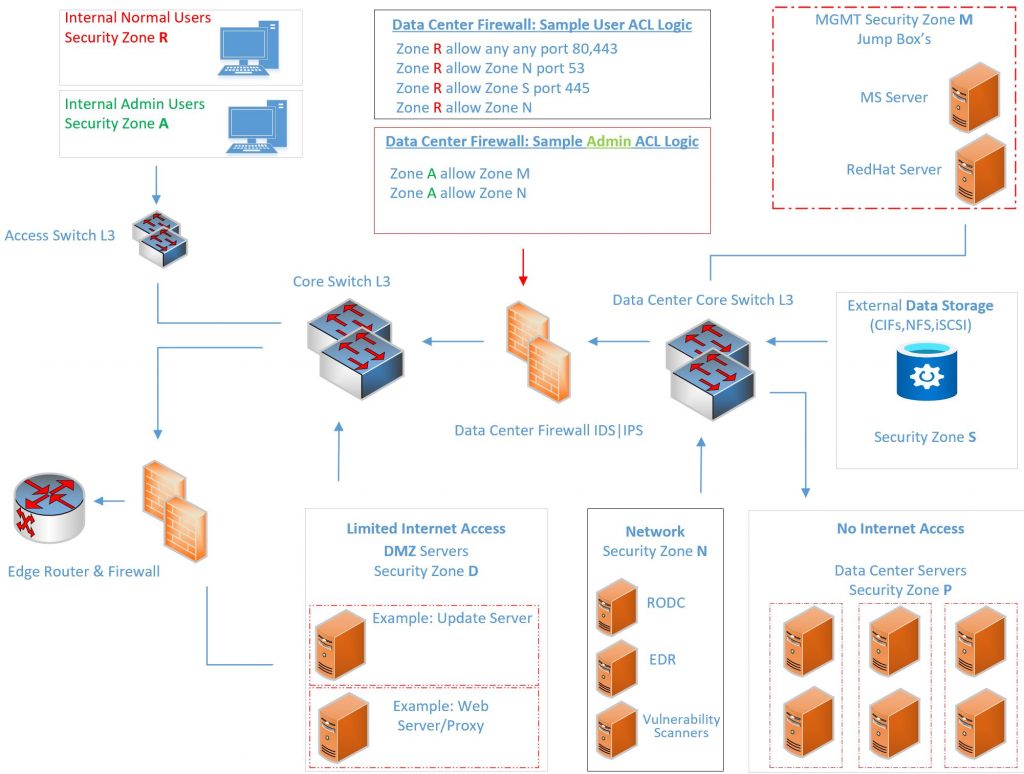
This post will be speaking to one of the 7 common security Zones as further illustrated below.
- Internal Users
- Internal Admin Users Zone
- Management Servers Zone
- Data Center Servers Zone
- Network Security Servers Zone
- Data Storage Zone
- DMZ Servers Zone
The above-mentioned Zones all have strict Access Controls (ACL’s) applied to them to control all aspects of egress and ingress traffic.
What you want to strive for in Zero trust implementations besides your 802.1X network access initiatives come in the form of “This system should only ever access these resources” and in some case even only for a certain time frame. Referencing the above diagram, I will just mention some key aspects for more detail on the approach.
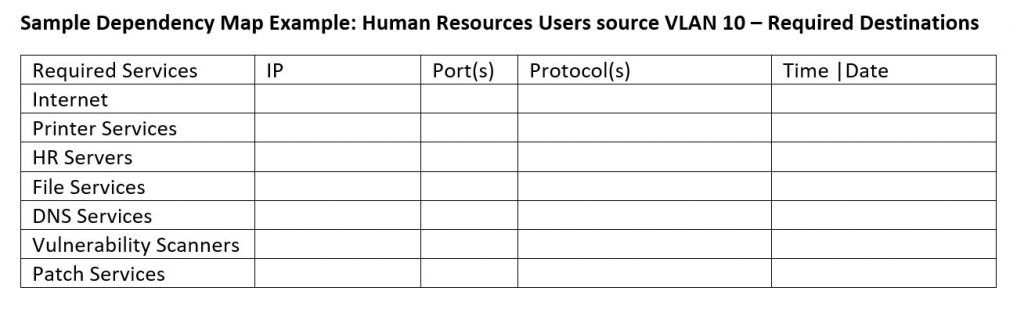
Example: Internal Users Security Zone
Logic: Your end users should only have access to specific network services that should be identified in a form of a dependency map on a per section bases such as HR, Marketing, Finance etc.
Once this information is gathered, at this time you can start creating policies to police the traffic. You can also enforce this configuration in Cisco with security groups tags (SGTs) and TrustSec as well as on the firewall. That would be a sample of Defense in Dept right? Now from more of a systems side, this is where RBAC comes into place to say these members are a part of this group and this group has access to these servers from 0600 to Midnight for example.
The Next example will illustrate a sample high level configuration of the placement and firewall rules for a VMware Update Server that needs to access the internet to pull down updates. When applying security controls for this type of requirement you would want to only allow a single object access to a single web site over SLL for a specific window of time.
First I usually draft up a plan of action in the form of proof of concept and walk through all the configuration steps that identify all of the dependences as well as supply this document to the change request. Below is an example at a very high level of what I mean.
Sample Requirement: VMware Update Server needs to access the VMware update site
VMware Update Server – should be in the DMZ Security Zone
DMZ rule to allows access – Specific URL – Time frame – Example every day from 0900-1200
DMZ rule to block all other access externally for the VMware Update Server object
Port Requirements – SSL only – Inspection Required – Logging enabled (Best practices)
Now that I have a rough idea of what needs to be accomplished, I can move into the implementation. This is of course the change request has been approved, following good change management practices.
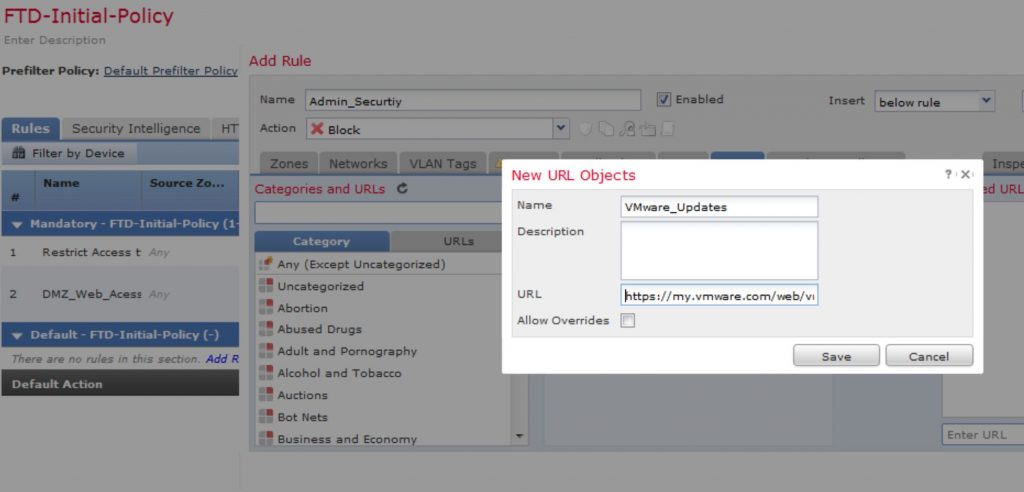
The below screen shots will speak to the configuration of the high points of this configuration leveraging Cisco Fire Power Threat Defense.
In the New Rule process, you specify specific details of what needs to talk to what, such as the URL Object creation
Screen shoot for the VMware website (https://my.vmware.com/web/vmware/downloads) object
The next screen shot is an example of the object placement on the destination side, identifying explicitly what URL will be allowed, the ports tab is where you will specify your SSL port requirement and the inspection tab is where you configure your inspection parameters.
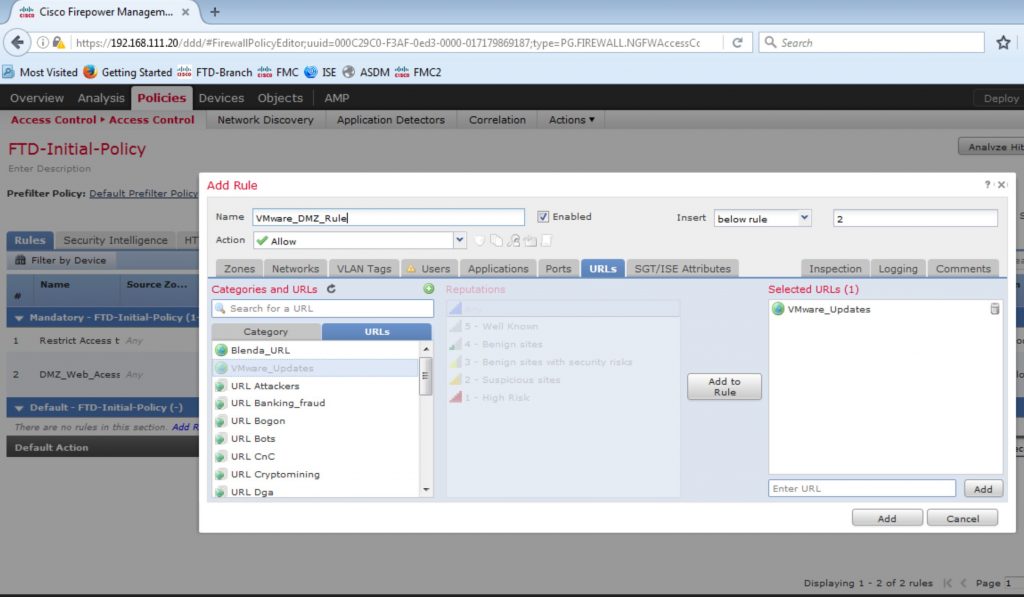
The below screenshot shows the placement of your Security Zones.
Here you are saying that the DMZ Zone Can Access the Outside Zone with several caveats
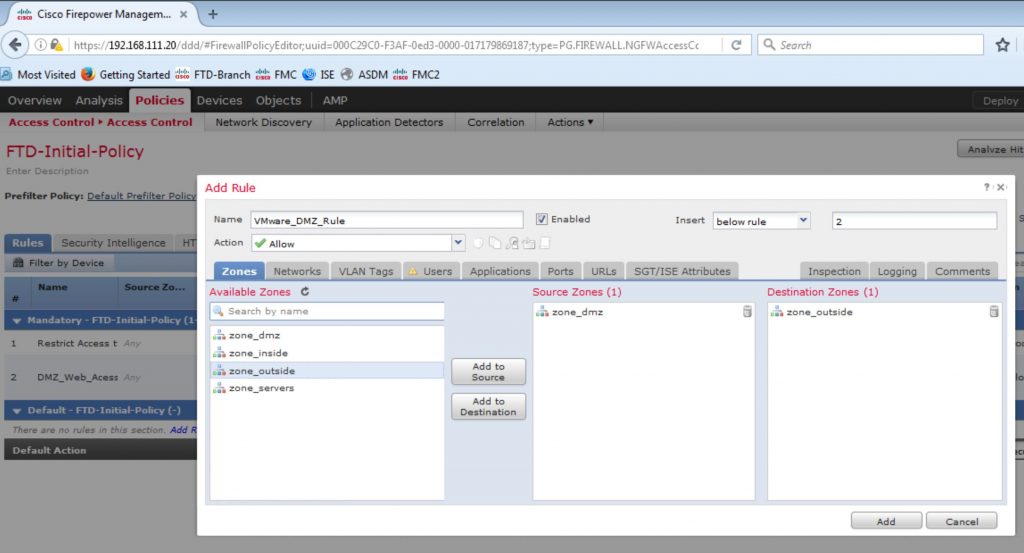
You will want to include the time constraints and other organizational requirements as well. Save, verify, deploy and test. Again, this was just and example including some screen shoots for visual reference. You also need to restrict access from the Management security zone to the DMZ Security Zone as well as the communication from the DMZ zone from the VMware update server back to the Data Center security zone.
Note:
In the upcoming post I will do some deep dives into the Cisco Secure Firewall, formally Cisco Threat Defense appliance. Covering rule creation, theory, and industry best practices behind the rules, referencing the NIST governing policies.