This post will go over the identification of the latest bug and fix actions for the Cisco UCS Firmware bundle 4.1 (3b).
Cisco Bug(s)
- CSCvx33064
- CSCvx23029
So, after successfully upgrading the Fabric and server firmware to version 4.1(3b) you log off and attempt to log back on and you receive the login attempt failed. With no changes to your underline security posture you ask yourself what just happened. Now your unable to log into to your UCSM.
The only way to gain visibility is via SSH or through a console connection
The first thing you want to check for and verify is the following
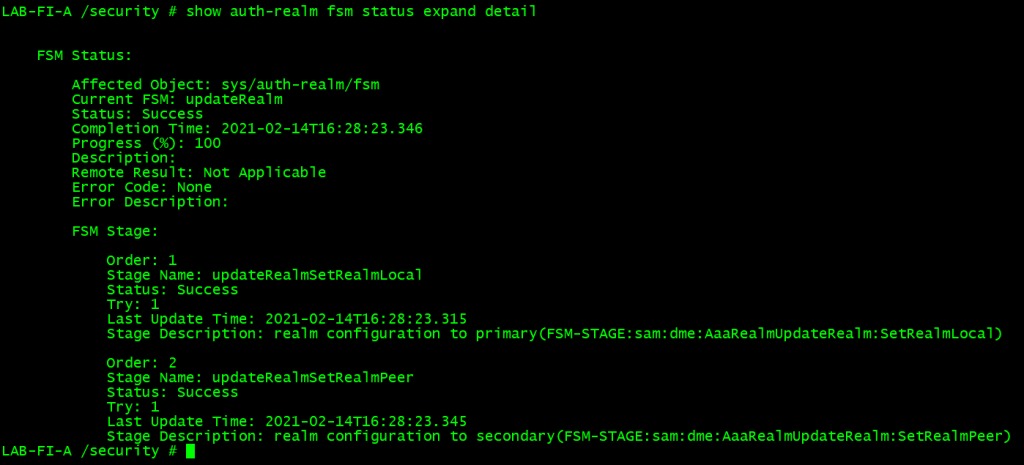
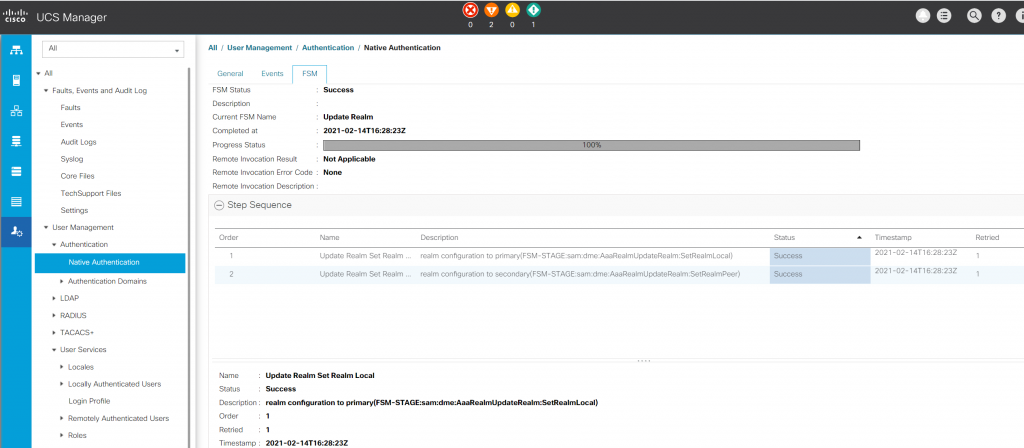
- The current status of the Finite State Machine (FSM)
Note: This is where you will see the incomplete status of the auth-realm process
This issue might also be triggered even if your Native Authentication Realm was set to LDAP prior to the update.
To resolve this, you will need to first clear the FSM process by changing your native authentication realm to local as show below
SSH Commands:
LAB-FI-A /security # show auth-realm fsm status expand detail
Commands to change the default authentication to local
LAB-FI-A /security # scope default-auth
LAB-FI-A /security/default-auth # set realm local
LAB-FI-A /security/default-auth # commit-buffer
The results of the above commands should provide the following output
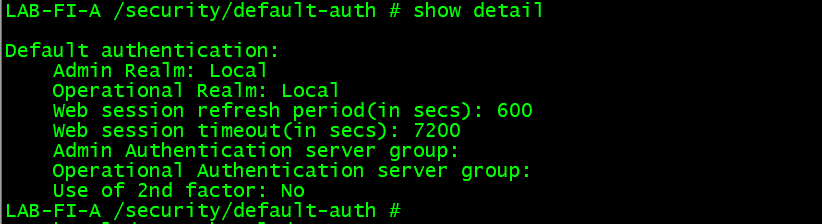
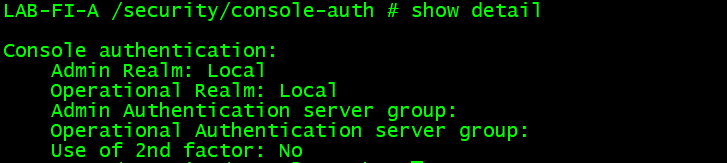
Commands to change the Console Authentication to local
LAB-FI-A /security # scope console-auth
LAB-FI-A /security/console-auth # set realm local
LAB-FI-A /security/console-auth # commit-buffer
The results of the above commands should provide the following output
UCSM Process:
From the Admin tab on the right-hand side of the screen select User Management, Authentication and Native Authentication
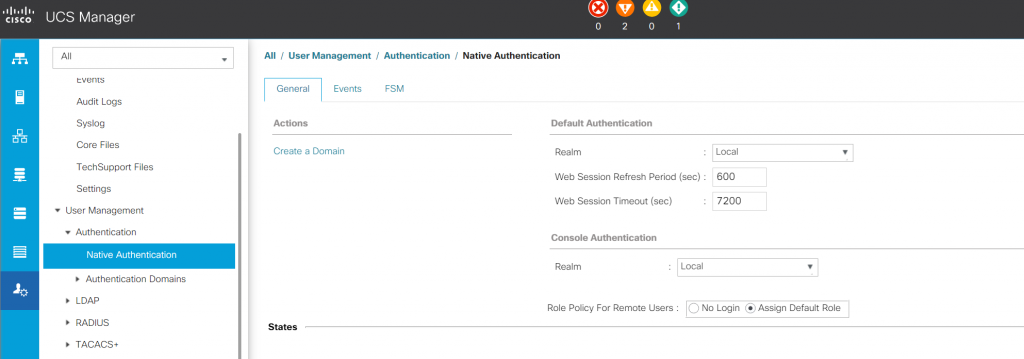
Once you have Changed both the Default Authentication and Console Authentication realms to default, select save changes and switch to the FSM tab and verify that the change was successful as shown below
Another issue I ran into after the 4.1 (#b) upgrade was the Cisco bug CSCvx23029 that still did not allow me access the UCSM. This bug does not like periods in the Authentication Domain name. So here you just need to remove the Authentication Domain and recreate a new one minus the period. My Authentication Domain name was named lab.local and was recreated as just lab minus the .local.
Note: your provider group will stay in place so you can delete the Authentication Domain and not have to recreate your provider. Once you recreate the Domain you just re associate the provide group.
You can subscribe to both defects via the Cisco bug search links provided below to stay up to date with all of the updates and recommendations with both bugs moving forward.
• https://bst.cloudapps.cisco.com/bugsearch/bug/CSCvx33064
• https://bst.cloudapps.cisco.com/bugsearch/bug/CSCvx23029