Why DNS Data Exfiltration is hard to detect and why you should care?
In this quick explanation of the topic, I will explain the fundamental aspects of DNS and Data Exfiltration via DNS Tunneling for baseline understanding and conclude with ways to detect and alert on such an attack. Note, most firewalls allow all DNS traffic to freely traverse the perimeter out of necessity, restricting or blocking DNS based traffic is simply not possible.
DNS Preface
Domain Name Service (DNS) is the global system for translating Internet Protocol (IP) Addresses into human readable domain names in its simplest form. DNS however is not as simple as that, the process behind the scenes that allow this translation to occur include three types of DNS queries, three DNS Server types, ten types of DNS records and over 20 RFC’s.
DNS Tunneling is the process of encoding data payloads in the DNS protocol queries and responses.
Data Exfiltration is the process of data leaving a system or network in an unauthorized manor.
DNS Facts to understand for threat hunting and log analytics.
Ports and Protocols
UDP & TCP Port 53 (UDP is the default protocol, TCP is the fall back when the packets are too large for a single UDP packet over 4096 bytes) Usually this behavior involves DNS Zone transferrers or the implementation of DNSSEC. The DNS protocol is a stateless protocol, as described in the RFC1035.
DNS Packets
In IPv4 the minimum IP packet size without any options and no upper-level protocol payloads is 20 octets in length. The maximum packet size without IP fragmentation is 68 octets (RFC 791). The largest packet that all hosts must be capable of processing is 576 octets. The maximum IP packet size in this protocol is 65,535 octets, as the IP header uses a 16-bit IP packet length field.
In IPv6 the minimum IP packet size is 40 octets. The maximum size of a packet without IP fragmentation is 1,280 octets (RFC 8200). The largest packet that all hosts must be capable of processing is 1,500 octets (RFC 8200). The maximum packet size is 65,575, based on the redefinition of the 16-bit packet length field to not include the 40 octet IPv6 packet header. There is also a Jumbo Payload option (RFC 2675) that uses a 32-bit packet length field, allowing for packet sizes with a 32-bit payload length excluding the IPv6 packet header.
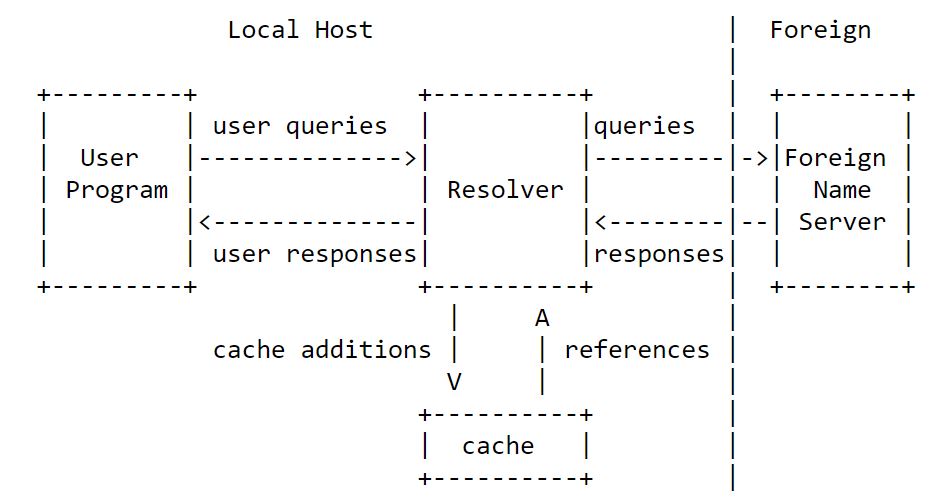
Based off the original DNS specification (RFC 1035), the below diagram represents the DNS process flow.
Ways to Detect DNS Tunneling and Data Exfiltration
First, you must understand and baseline what your systems and network behavior look like to understand what bad or anomalous behavior looks like. In a more realistic setting many organizations if any cant just hit a magic reset button and say let us start over from stretch to get that much needed baseline view, so what is the best approach now you ask?
Now more than ever cyber security professionals need to take a step back and revisit the fundamental aspects of all of the services running on there network and deep dive into them such as this post to understand what right looks like at the protocol level. With this understanding you will be more efficient at log analytics and defense in depth design.
What to look for
You want to monitor your network for changes in resource type behavior, which can be an early sign of data exfiltration. Examine the results for changes in types of records being queried. Both A records and TXT records should be observed carefully as these are commonly used in command and control or exfiltration activities. Detection can be accomplished by analyzing payloads and traffic.
Review the size and number of DNS packets being transmitted over your network.
Analyze your network for Beaconing activity, this is occurs when a compromised host ‘checks in’ with the command infrastructure, possibly waiting for new instructions or updates to the malicious software itself.
You want to monitor your network for large DNS packets or an unusually high volume of DNS packets, both of which can be an early sign of data exfiltration.
For example, many common domains (www.google.com and www.facebook.com) have a small query string length and will have a small query count. If, however, the malicious software opens a sensitive
Payload analysis detects malicious activity based on a single request and its associated responses are analyzed for tunnel indicators. Software such as Wireshark are best known for this type of analysis.
DNS Size limits (RFC 1035)
labels 63 octets or less
names 255 octets or les
TTL Positive values of a signed 32-bit number
UDP messages 512 octets or less
A few ways to Mitigate the DNS Tunneling attack.
- Implementing network inspection via security products where DNS traffic can be analyzed.
- Limiting clients DNS traffic and creating rules triggered when a specific threshold is reached.
- Set up and secure dedicated DNS servers.
- Create network segmentation via SDN solutions.
- Configure firewalls rules on specific ports.
- Blocking unauthorized channels
- Implementing data loss prevention (DLP) policies
- And finally, raising awareness for employees about these types of attacks is Key.
Note: For additional information please check out DNScat or DNScat2 as this software is well known for establishing DNS Tunnels for Data exfiltration. The mindset of thinking like and attacker to defend against the attack is still very much required.
Disclaimer
The advice and information listed above is for educational purposes only. This was not an all-encompassing list of ways to mitigate any cyber security related attacks.