How to provide additional layers of security with Web sessions
One of the latest security exploits has been in the area of a popular web browser Google Chrome. The Google chrome browser is feature rich providing a world of capabilities to explore and make ones browsing experience more connected and functional. Of course, with this comes the opportunity for creativity in the form of exploiting security loopholes.
Google has released the below comment stating they will address the current vulnerabilities in the next release (88.0.4324.150) In the up coming weeks
Chrome Releases: Stable Channel Update for Desktop (googleblog.com)
NIST is tracking the following CVE’s related to the latest releasable version of Google Chrome
CVE-2021-21143 (High)
CVE-2021-21127 (High)
CVE-2021-21126 (Medium)
CVE-2020-16039 (High)
In this post I will explain some of the high-level Defense in Dept best practices to implement to strengthen your security posture. First to explain wheat is a browser extension. Browser extensions modify the core browser user experience by changing the browser’s user interface and allows interaction with other web sites. Many extensions interact extensively with arbitrary web pages, creating a unnecessary attack surface that can be exploited for underline vulnerabilities.
Securing your Browser sessions The Google Chrome extension
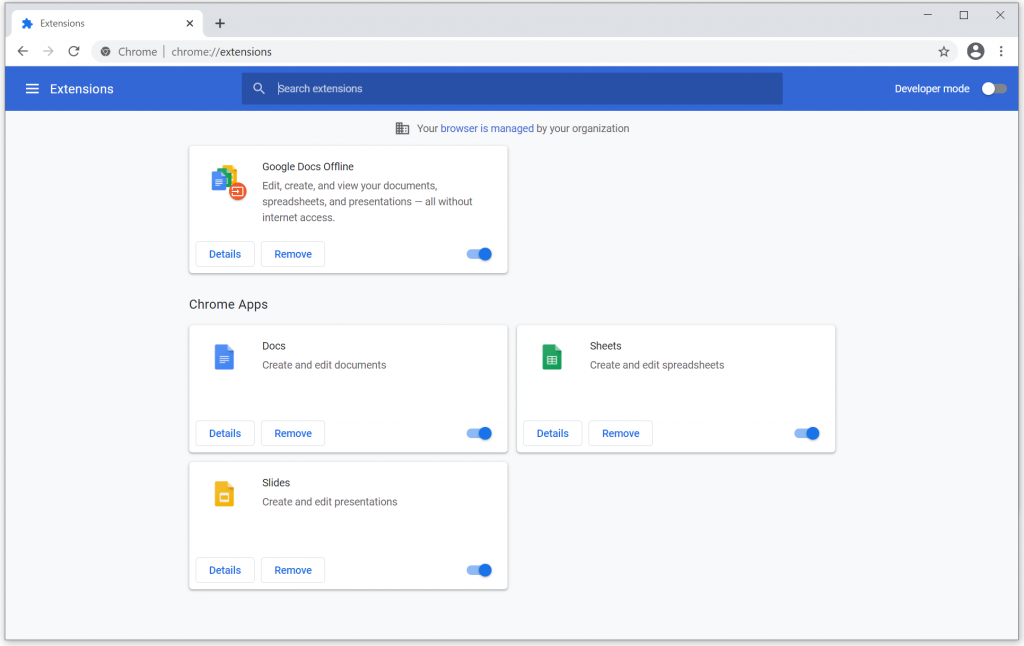
The Next screenshot will display the settings on an individual user’s browser settings that will be locked down
Security Hardening Fix action:
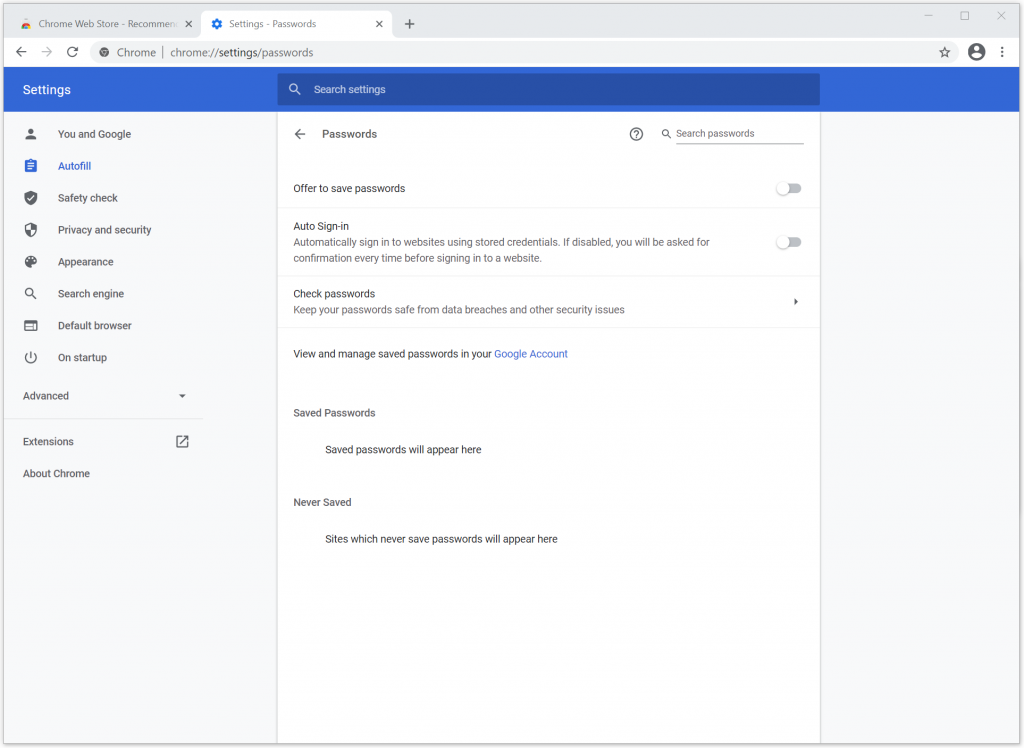
Disable caching of passwords and auto-completion of username and passwords in Internet Explore via Windows Group Policy.
First you will need Chrome templates (ADMX)
Navigate to Start > Run: gpedit.msc. (Or run gpedit.msc in your terminal)
Navigate to Local Computer Policy > Computer Configuration > Administrative Templates.
Right-click Administrative Templates, and select Add/Remove Templates.
Add the chrome.adm template
In the Group Policy Editor, open the template you just added and change the configuration settings.
The Security Policies that speak to our main goal here are follows
- Allow and block Apps
- Install sources
- Allowed app types
- Block extensions by permission
- Chrome web store home page and permissions
The next defense in dept best practice will be to leverage a capability native to Microsoft called App Locker. This is a another Group policy based solution that will allow you to deploy in Audit only mode to first capture what applications are being executed on your end points to include web browsers and once you have the current state of application execution then you will want to whitelist allowed applications only. The enforcement of this new capability is done via the AppLocker console via the following configuration steps.
AppLocker Enforcement Configuration steps (High Level)
From the AppLocker console, right-click AppLocker, and then click Properties.
On the Enforcement tab of the AppLocker Properties dialog box, select the Configured check box for the rule collection that you are editing, and then verify that Enforce rules is selected.
Click OK.
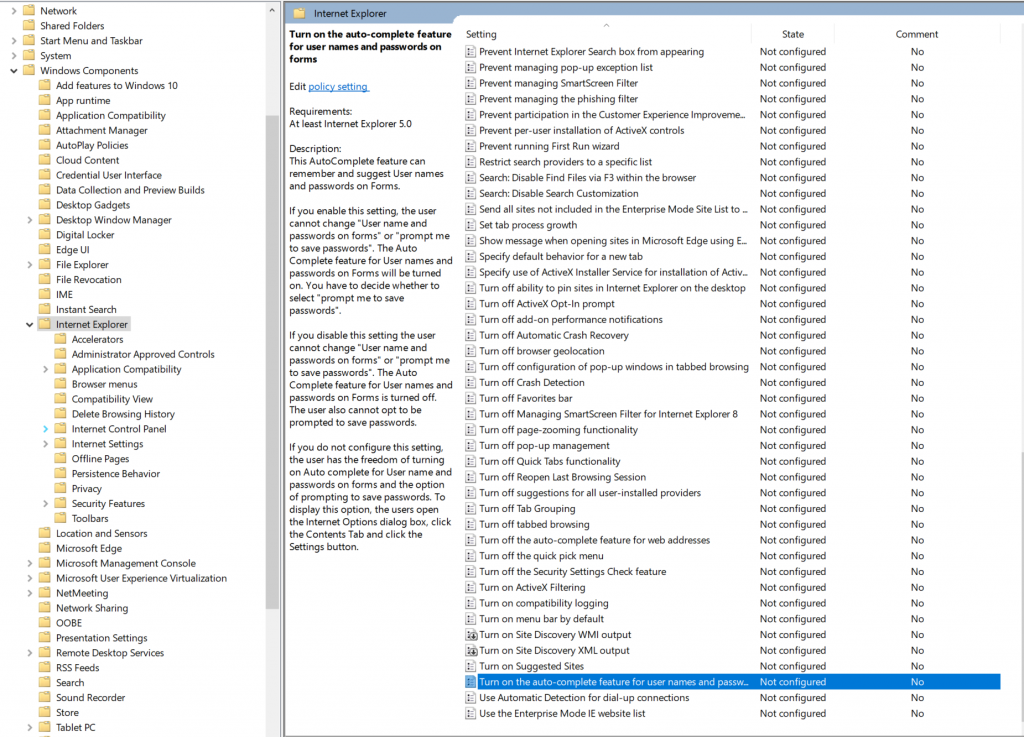
The Same core principles apply to securing Internet Explores extensions. The Group policy method is identified below.
For Internet Explore the Process is below.
Group Policy Editor Setting configuration:
User Configuration > Policies > Administrative Templates > Windows Components > Internet Explorer
Here, you can disable (Turn on the auto-complete feature for user names and passwords), as shown below
Note:
The above Security solutions are not a complete list of available applications or approaches. There are several other security solutions such as Microsoft Desired State Configuration and other File Integrity applications available to name a few. The solutions provided were some that are just easier to implement in a short time notice if not already in use.